
Address bar spoofing in Firefox Lite for Android ...and the idiocy that followed
Date reported — 2019-08-29
Summary
Firefox Lite 1.9.2 for Android and earlier suffer from exhaustive Address Bar Spoofing, allowing attackers to potentially trick a victim into visiting a malicious domain for legitimate domain name. Firefox Lite is almost installed on more than 10M devices.
Impact
URL Address Bar spoofing is the worst kind of phishing attack possible because it's the only way to identify the site which the user is visiting for a non-technical user. URL address bar is the only way to trust a website and if this indicator is hijacked, the whole security of any normal user will be compromised.
Explanation
The address bar can be spoofed by a crafted javascript page with setInterval() function which executes pwn() function which ultimately reloads target URL in every 10ms.
Proof of concept (POC)
- Opening Firefox Lite; Latest version i.e.1.9.1 (13361)
- Spawning a HTTP web-server with the attached payload i.e.
spoof.html - Loading the page e.g http://10.10.10.10/spoof.html
- URL gets spoofed and shows contents of
spoof.htmlwhile URL points at https://www.mozilla.org/en-US/
Video demo — https://youtu.be/wzpteHxAQSw
Expected behavior
The browser should successfully redirect to the target website.
Reply from Mozilla
Quickly acknowledging, validating, and resolving submitted issues while recognizing the researcher's effort is vital for successful vulnerability coordination, but the report didn't got any attention after initial triage and half-hearted discussion.
...11 months later
I got fed up after waiting for months, eleven months to be exact. I emailed security@mozilla.org asking them to look at the stale bug report.
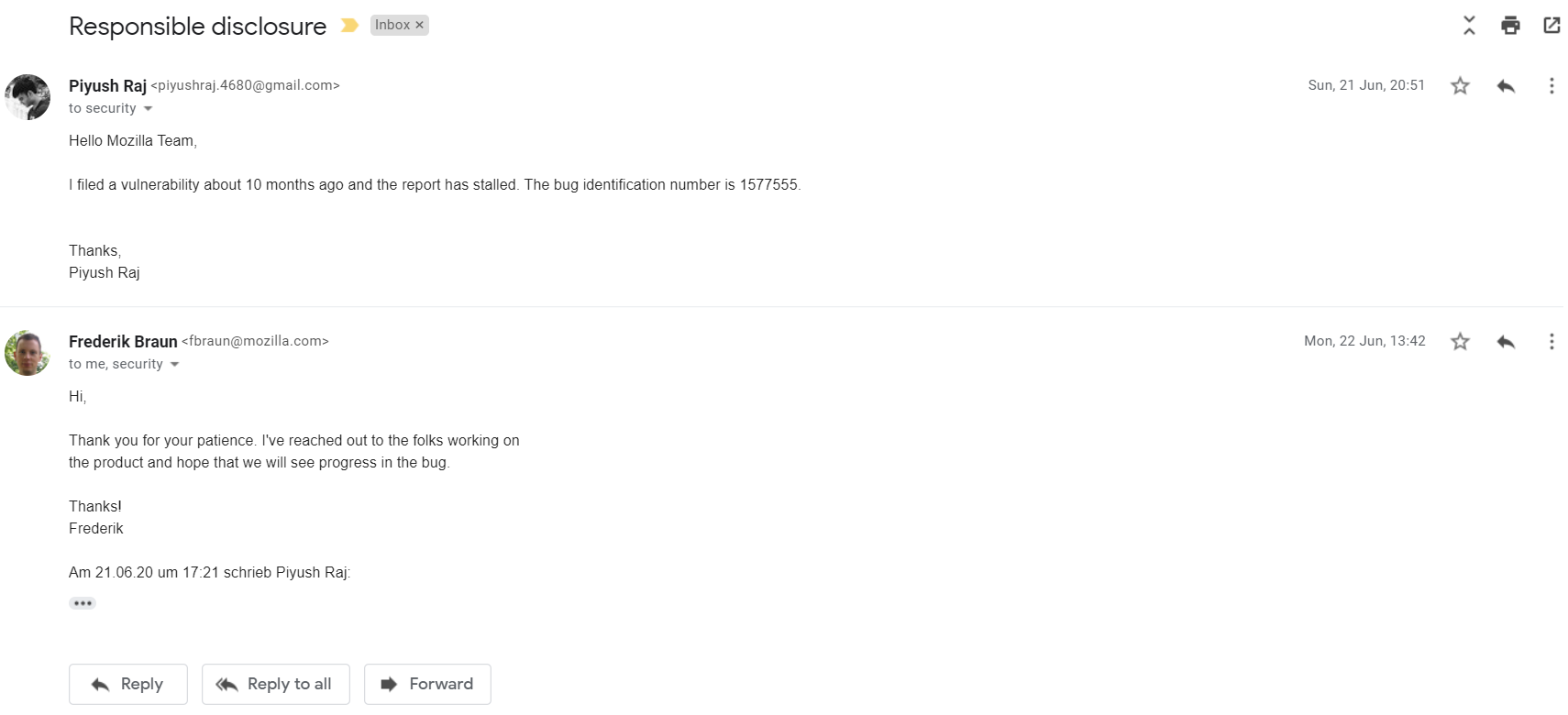

Frederik helped to re-initiate the staled report. This is what happened afterwards —
Thanks for the notification, --REDACTED--! we'll prioritize this issue in the sprint planning later today. --REDACTED--
Hi folks,
Per the given information and testing result, this issue is reproducible only on old webview versions (70).
Users has to update Chrome and Firefox Lite to latest version so that they get better security.
And then the coming tricky problem is we don't have good position to prompt users to update their Chrome.
As we have very small user base hanging on that (or older) version so the impact is fairly limited.
That said, we don't see immediate action to take on this issue.
Lingering the report for 11 months while the Google's webview versions regularly updated; establishing low impact with a ridiculous reason. It's like saying — "Oh yeah, there's RCE possible but we don't use the software which has the bug you know, so the impact is fairly limited".
I don't think the reply needs any more explanation. I leave it up to you to judge the response. I'm not gonna do anything now. Let's see what happens.
Peace out.